Showing all 50 results
-
$39.95
Fake ID Australia Passport
-
$39.95
Fake ID Australia Queensland
-
$39.95
Fake ID Australia Victoria
-
$39.95
Fake ID Austria
-
$39.95
Fake ID Bahrain
-
$39.95
Fake ID Bangladesh
-
$39.95
Fake ID Brazil
-
$39.95
Fake ID Canada
-
$39.95
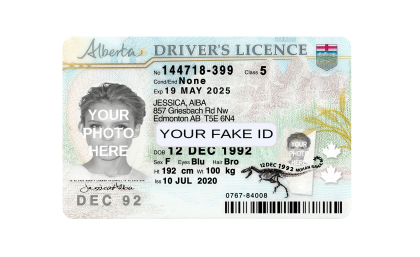
Fake ID Canada Alberta
-
$39.95
Fake ID Canada British Columbia
-
$39.95
Fake ID Canada Manitoba
-
$39.95
Fake ID Canada Nova Scotia
-
$39.95
Fake ID Canada Ontario-V1
-
$39.95
Fake ID Canada Ontario-V2
-
$39.95
Fake ID Canada Passport
-
$39.95
Fake ID Canada Quebec
-
$39.95
Fake ID China
-
$39.95
Fake ID Czech Republic
-
$39.95
Fake ID Estonia
-
$39.95
Fake ID Finland
-
$39.95
Fake ID France
-
$39.95
Fake ID France Passport
-
$39.95
Fake ID Front and Back With Selfie
-
$39.95
Fake ID Front and Back With Selfie-2
-
$39.95
Fake ID Front and Back With Selfie-3
-
$39.95
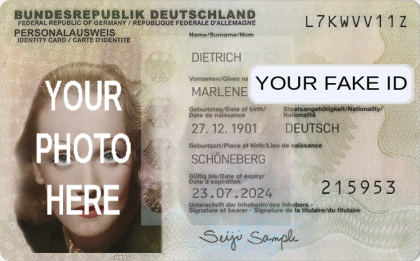
Fake ID Germany
-
$39.95
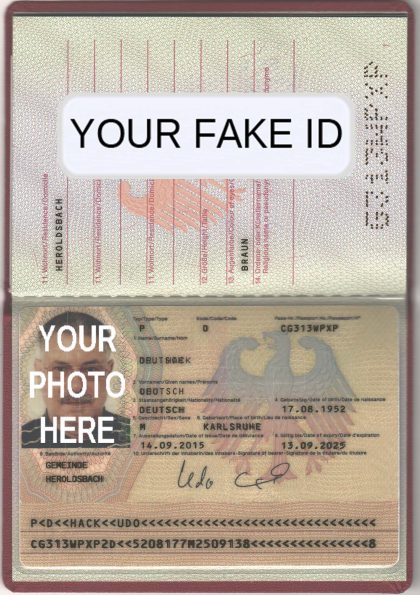
Fake ID Germany Passport
-
$39.95
Fake ID Hong Kong
-
$39.95
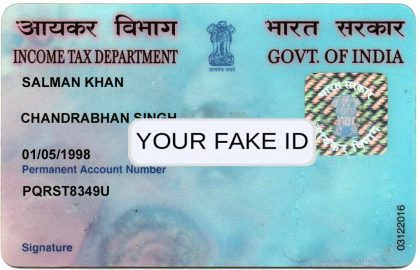
Fake ID India
-
$39.95
Fake ID Ireland
-
$39.95
Fake ID Italy
-
$39.95
Fake ID Lithuania
-
$39.95
Fake ID Malaysia
-
$39.95
Fake ID Netherlands-V1
-
$39.95
Fake ID Netherlands-V2
-
$39.95
Fake ID Poland
-
$39.95
Fake ID Portugal
-
$39.95
Fake ID Romania
-
$39.95
Fake ID Singapore
-
$39.95
Fake ID Slovakia
-
$39.95
Fake ID Slovenia
-
$39.95
Fake ID South Africa ID Card
-
$39.95
Fake ID Spain
-
$39.95
Fake ID Sweden
-
$39.95
Fake ID Switzerland
-
$39.95
Fake ID Thailand
-
$39.95
Fake ID Turkey
-
$39.95
Fake ID United Arab Emirates
-
$39.95
Fake ID United Kingdom
-
$39.95
Fake ID Western Australia
When to Use a Fake Name to Protect Anonymity
A pseudonym, pen name or fake name is an alternative identity used for writing. People have used them since there has been an ability to share writing among groups. Facebook’s “real name” policy has put those using pseudonyms at great risk, from abusive former partners to politically-motivated attacks and threats of physical violence.
Online Stalking
Online stalking refers to unwanted contact and surveillance via social media platforms, internet searches and other digital methods. Perpetrators use technology to monitor victims and harass or even threaten them in this way; if you feel you may be being stalked online it is important that if this is occurring to take the following steps: Create a safety plan. Consider speaking to an advocate for help.
Save copies of all communications that could be considered threatening or harassing, such as text and voice messages you receive on your phone, emails and chat logs from anyone stalking you, screenshots from computer monitors used as evidence against stalking and screen shots taken with your webcam to document harassment incidents. A fake identification also known as a fake id may be needed to better enhance this for some people. Ensure these documents are backed up regularly and stored safely such as an external hard drive or removable memory stick.
Inform your family and friends of your situation, explaining your fears and symptoms so they can offer assistance if necessary. Warn coworkers, schoolmates and on-site security staff about what you are going through as well; ask them to keep an eye out for any individuals matching this description and contact either yourself or the police if they ever spot anyone matching it.
Change your login name and password on all online accounts to something more discreet, change your email address away from including personal data, and disable the location services of your phone if someone may be tracking you. Check for information published about you by a stalker online, such as blogs or website comments. If they have harassed you by publishing harmful material in these spaces, make a complaint against their moderators/managers as soon as possible – often they can block their IP address or remove posts altogether.
Be wary when posting any personal or intimate photographs to social media accounts. Your friends could potentially share these without your knowledge, creating the possibility for misuse. Also consider closing any unused accounts.
Harassment
Are You Being Harassed Online? | UAB When experiencing cyber harassment online, people may opt to create fake names in order to protect against harassment and protect their personal privacy. Many people have taken this to another level by using a fake identification also known as a fake id. Examples of cyber harassment may include stalking, sending harassing messages via messaging platforms or cell phones; outings; sharing personal data of someone in order to embarrass or threaten them (also known as “doxing”) etc.
When students, staff members, postdocs or academic appointees experience harassment it is vital they document all incidents as thoroughly as possible. This should include saving threatening or harassing messages as well as screenshots of text messages and phone calls to document all times, places, people involved in incidents that involve harassment – this may help in identifying harassers as well as dealing with criminal threats more efficiently.
The University provides academics with several resources for use, such as temporarily disabling one’s profile or contact information from University websites. Faculty members and instructors should take multiple precautions when teaching courses that require significant virtual interaction; these measures may include:
If a worker feels unsafe at their workplace, they can report this behavior to their supervisor or administrative leader and depending on its severity, University resources will provide assistance and address any underlying concerns. Some people find it necessary to use a fake identification also known as a fake id for added benefits. Likewise, if someone is being bullied or harassed on social media platforms such as Facebook and Instagram, they can often modify their settings to “mute” those responsible and prevent them from viewing any of their posts, although they may still see posts posted by groups or accounts they belong to that have added them.
EFF was shocked to learn that Facebook’s implementation of its “real names” policy had such an adverse impact on LGBTQ individuals, particularly drag performers, that many were forced to reveal their real legal names for Facebook to verify them as authentic users. Since then, Facebook has apologized and clarified that “authentic” names don’t necessarily correspond with people’s legal names; therefore they can continue using stage monikers without having their names revealed by them.
Defamation
Internet makes it easy for individuals and companies alike to defame one another, damaging reputations and leading to financial loss. Defamatory statements can come through online reviews, social media posts or news articles; if this has happened to you it is essential that you seek immediate legal advice; our team has extensive experience helping restore reputations as well as seeking damages.
Step one of a defamation case involves providing proof of false statements made and their impact; this may involve showing emails, screenshots or downloads showing this conduct. Once evidence of defamatory conduct exists, step two must address its impact – be it financial loss through missed earnings, emotional suffering or psychological trauma. Depending on the nature and extent of damages sustained from defamatory statements made against you, compensation could be available ranging from small compensation awards up to significant payments from court settlements.
Defamatory statements published anonymously can be difficult to track down. This type of endeavour can be enhanced with a fake identification also known as a fake id. When this occurs, some groups work with Internet Information Specialists who use various tools and techniques to trace those responsible – this can include IP tracking, registrant searches and even social media forensics.
Anonymity online can be challenging but not impossible to attain, and it is crucial that individuals understand there are laws against Strategic Lawsuits Against Public Participation (SLAPP suits). These suit can often be used by powerful players within government, industry and communities against critics to stop their work from progressing further – this applies particularly to bloggers and activists who come under attack from powerful entities within these sectors.
Anonymity can be an invaluable defense mechanism against defamation from those with personal grudges against them, but it does not offer complete protection for both privacy and safety. Social media offers some protection with pseudonymous profiles; however, take care not to disclose confidential details that could help identify you directly; additionally if sued for slander using such pseudonyms they may need to reveal their real identities in court in order to defend themselves successfully.
Identity Theft
While privacy and anonymity often go hand-in-hand, sometimes one takes precedence over the other. Some individuals may need anonymity (or pseudonymity) when communicating online; on the other hand, privacy focuses on safeguarding private information. While financial identity theft may be well known, synthetic identity theft has also seen an upswing. Other people will take this to a higher level by using a fake identification also known as a fake id. This form of ID fraud involves identity thieves combining stolen credentials from real identities into new personas for use in perpetrating credit card and insurance fraud, among other crimes.
To protect our personal privacy, using fake names is often essential. Aliases for social media, untraceable networking services (Tor), and random usernames all help ensure our identities remain anonymous. Please note this differs from security which involves keeping information separate from us; security involves using proxy servers, changing internet protocol settings on computers to encrypt all transmitted data, never entering personal details into public places and never sharing such details publicly – hence why anonymity can often be described as being worn like a mask. Some people will want to take this to another level with a fake identification also known as a fake id.
How to Use a Fake Name When Surfing the Internet to Avoid Stalking
Protect yourself online by being mindful about what information you share online and being aware of the privacy settings on all social media accounts and instant messaging services used by family and friends. Change all passwords to ones that will be difficult for cyberstalkers to figure out, and pick gender-neutral screen names. This endeavour can be enhanced with a fake identification also known as a fake id. Also ensure your internet service provider, cell phone service and any other online providers have appropriate privacy policies that prevent cyberstalking.
Use a Fake Name
Stalking is the repeated and unwanted contact that causes fear and intimidation to someone, sometimes to the point of physical violence. Stalking can take place both online and in-person. Use an fake name or pseudonym on social media and other sites to protect yourself from online stalkers, like your initials, middle name or older family name. Also make sure your privacy settings allow only certain people to view your profile.
Computer stalkers can gather plenty of information about you by Googling your name, searching your photos and seeing who likes you on Facebook – they could even track your cell phone location! If you believe you’re being stalked, keep a journal detailing dates, times and witnesses so it may help law enforcement and prosecutors with their investigations. Also notify friends, neighbors and coworkers so they can look out for suspicious activity in the area.
Change Your Passwords
Cyberstalkers can gain access to your email and social media accounts if they know your passwords. While you can change them yourself, it’s best done from a device not being monitored by your stalker, such as work computer or public library computer. Be mindful that stalkers may collect data about you online – through search engines, chat rooms, blogs and social media – as well as using spyware installed on computers, phones or GPS tracking devices attached to vehicles. This can be enhanced with a fake identification also known as a fake id for some people. As part of monitoring how people perceive you online it’s wise to regularly conduct an Internet search of your name to identify where your information appears online.
Make sure that your ISP, cell phone service provider and instant messenger (sometimes known as internet relay chat ) networks all adhere to an acceptable privacy policy that prohibits cyberstalking. Furthermore, save all threatening or harassing messages, hang-up calls and public sightings as evidence against cyberstalking. Whenever possible use an email account without personal data in its user name and choose gender-neutral aliases when posting online.
Change Your Email Address
Change of email address can help prevent cyberstalking. Try getting a private, fake name or pseudonym based email that does not reveal personal details such as age or name; also consider gender neutral screen names when online; use secure passwords regularly and frequently update them; ask friends not to reveal personal details to any stranger.
An effective measure is to Google yourself frequently and see what sort of personal details about you can be found online, as well as conducting similar checks for family and peers. Inform them if someone appears to be stalking you; ask them not to release any personal data regarding yourself. A fake identification also known as a fake id may be needed to better enhance this for some people. Keep a log or journal of all contacts between yourself and the stalker, including text messages, voicemails, letters and packages sent back and forth between them. This could serve as evidence should you decide to call the police.
Change Your Social Media Accounts
Cyberstalking is an increasingly prevalent issue that includes individuals following their targets on social media, sending emails or text messages, or even infiltrating devices they own to spy on them. An internet search will reveal much information about their targets including home addresses, phone numbers and credit card details – providing stalkers with plenty of evidence against their victim(s).
Stalkers can glean a lot of information by searching their target’s name in chat rooms, forums and other online communities; they may even use GPS devices to pinpoint physical locations. If you suspect you’re being stalked, it is imperative that you take immediate steps. Inform family, friends and supervisors as well as creating a safety plan with log of incidents; save all texts, emails and screenshots created in your name by your stalker – this may prove valuable evidence in case a investigation takes place.